Search-like simplicity for complex security architecture.
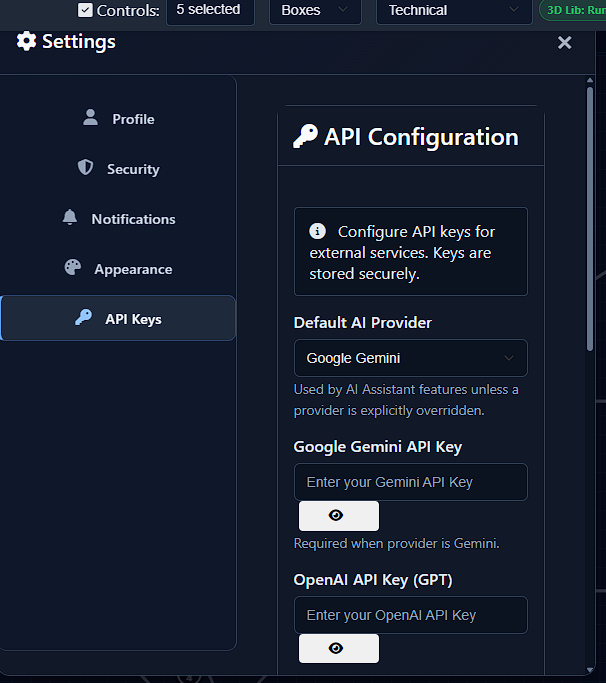
Model your network, run threat analysis, map controls, generate reports, and operationalize to cloud workflows from one dark-mode workspace.
Model your network, run threat analysis, map controls, generate reports, and operationalize to cloud workflows from one dark-mode workspace.
A complete architecture workflow from design to security validation and cloud-ready delivery.
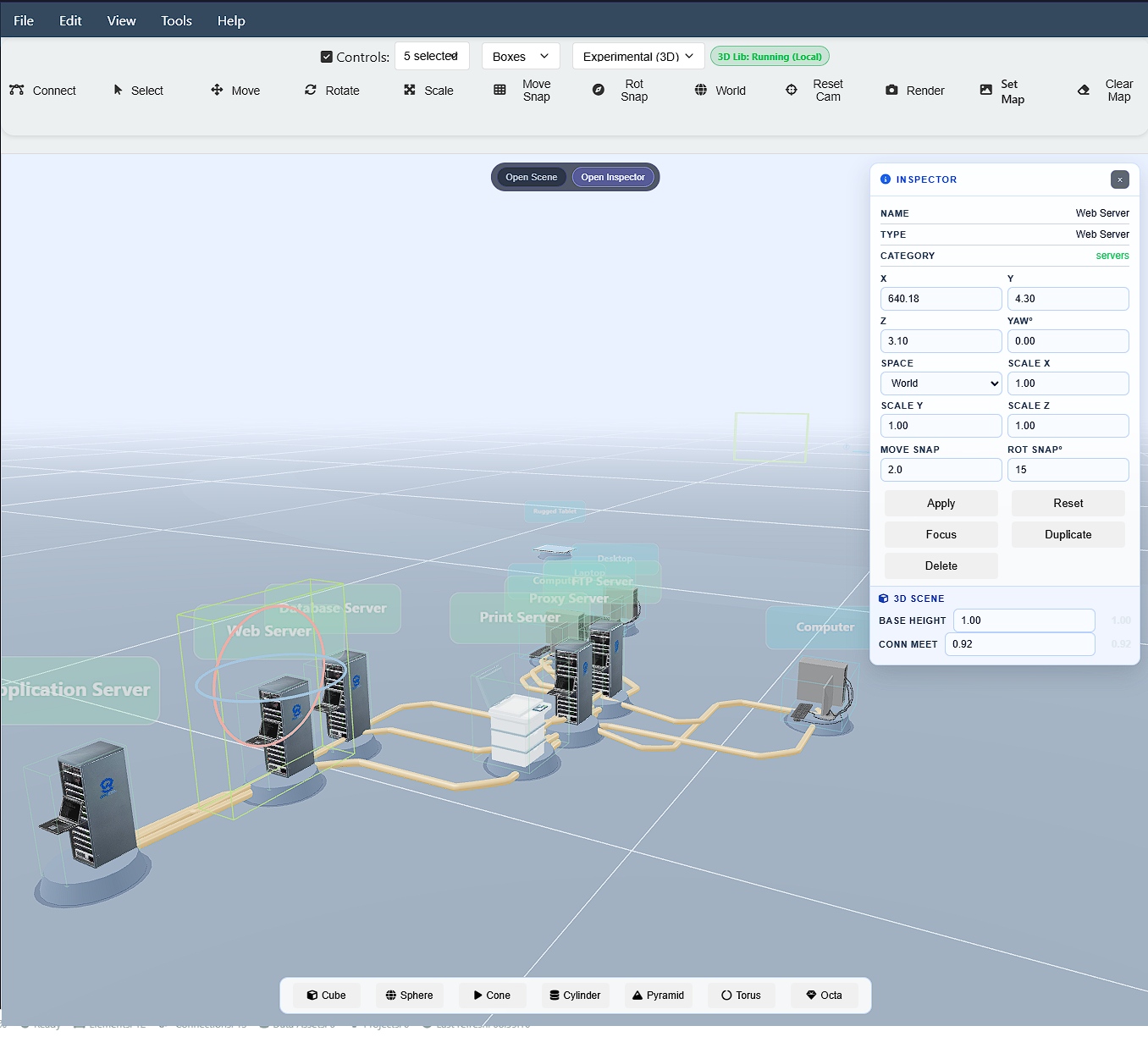
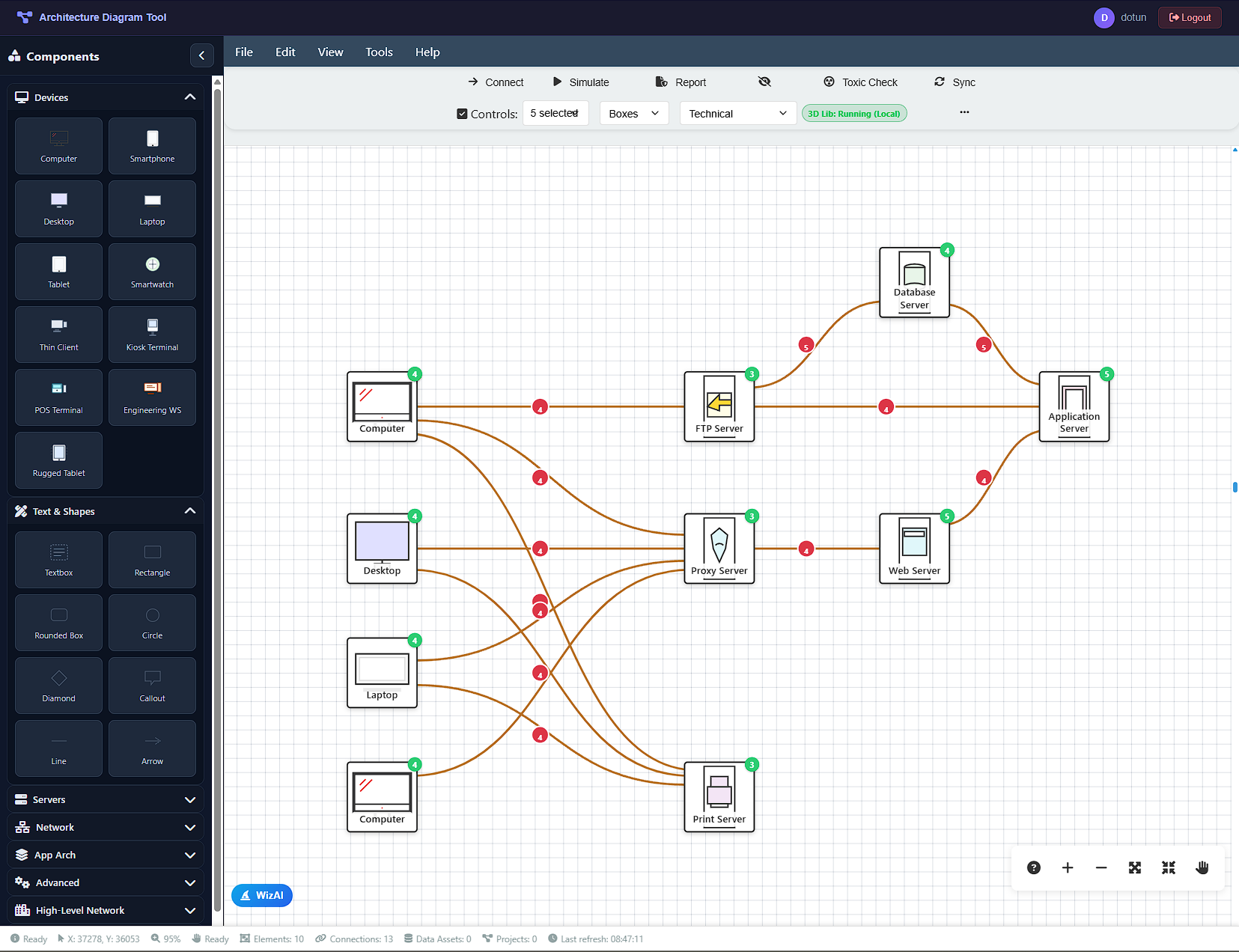
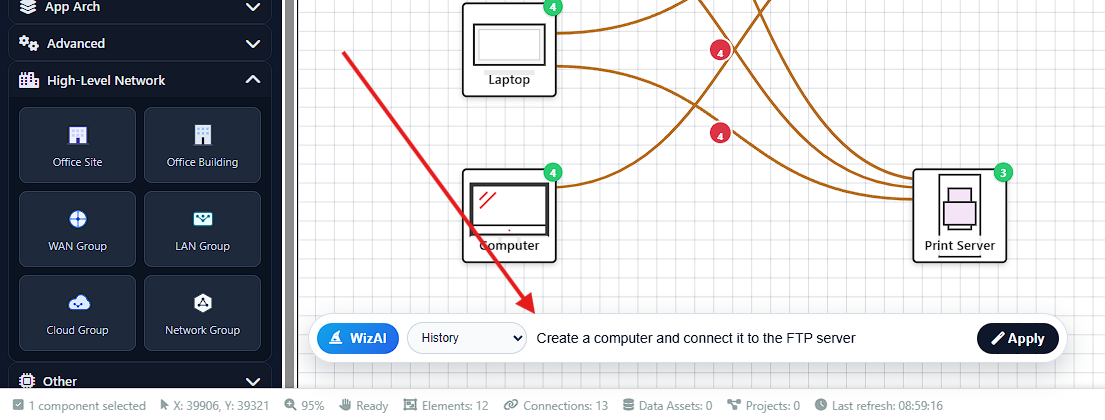
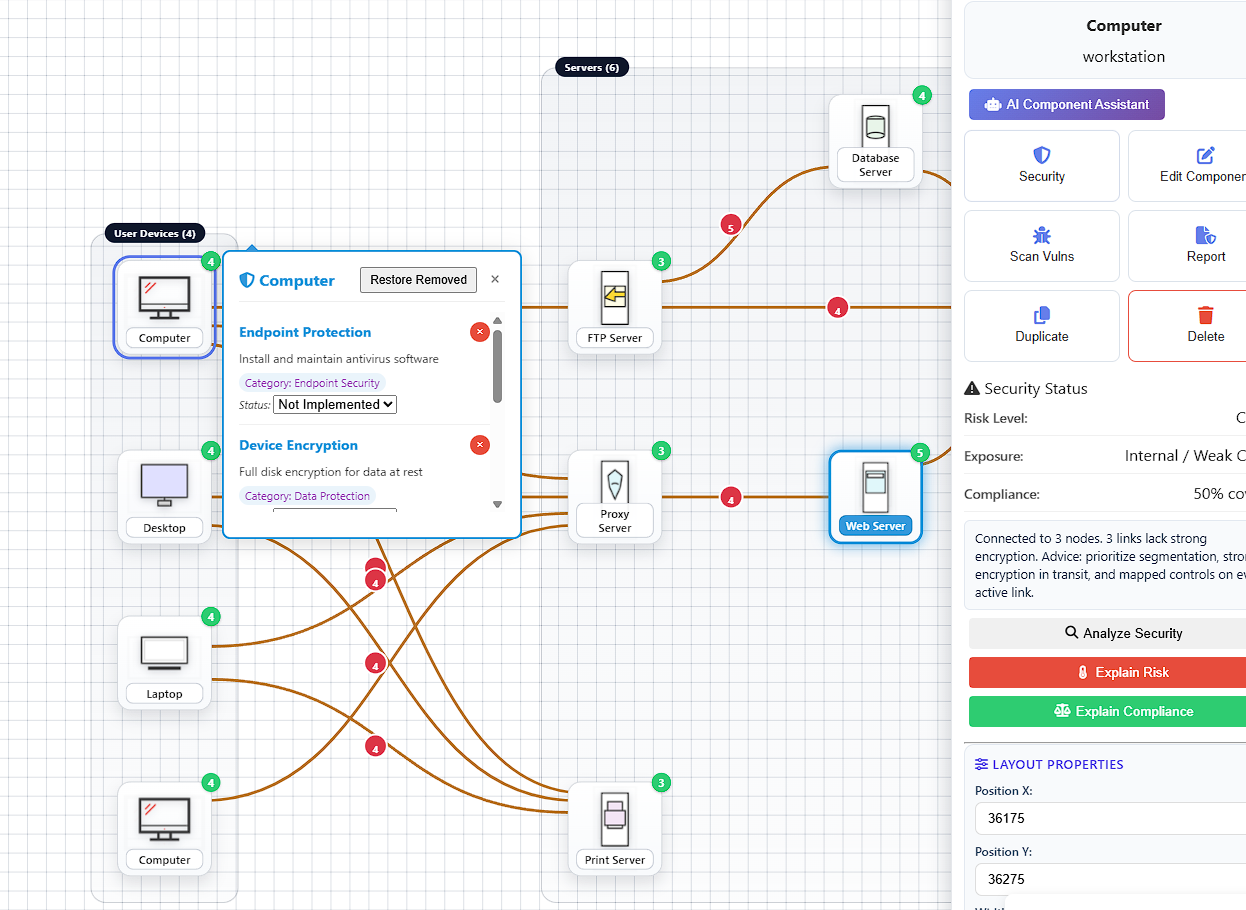
Build architecture with reusable components, rich connectors, and structured metadata.
Generate diagrams and get contextual recommendations directly inside your workflow.
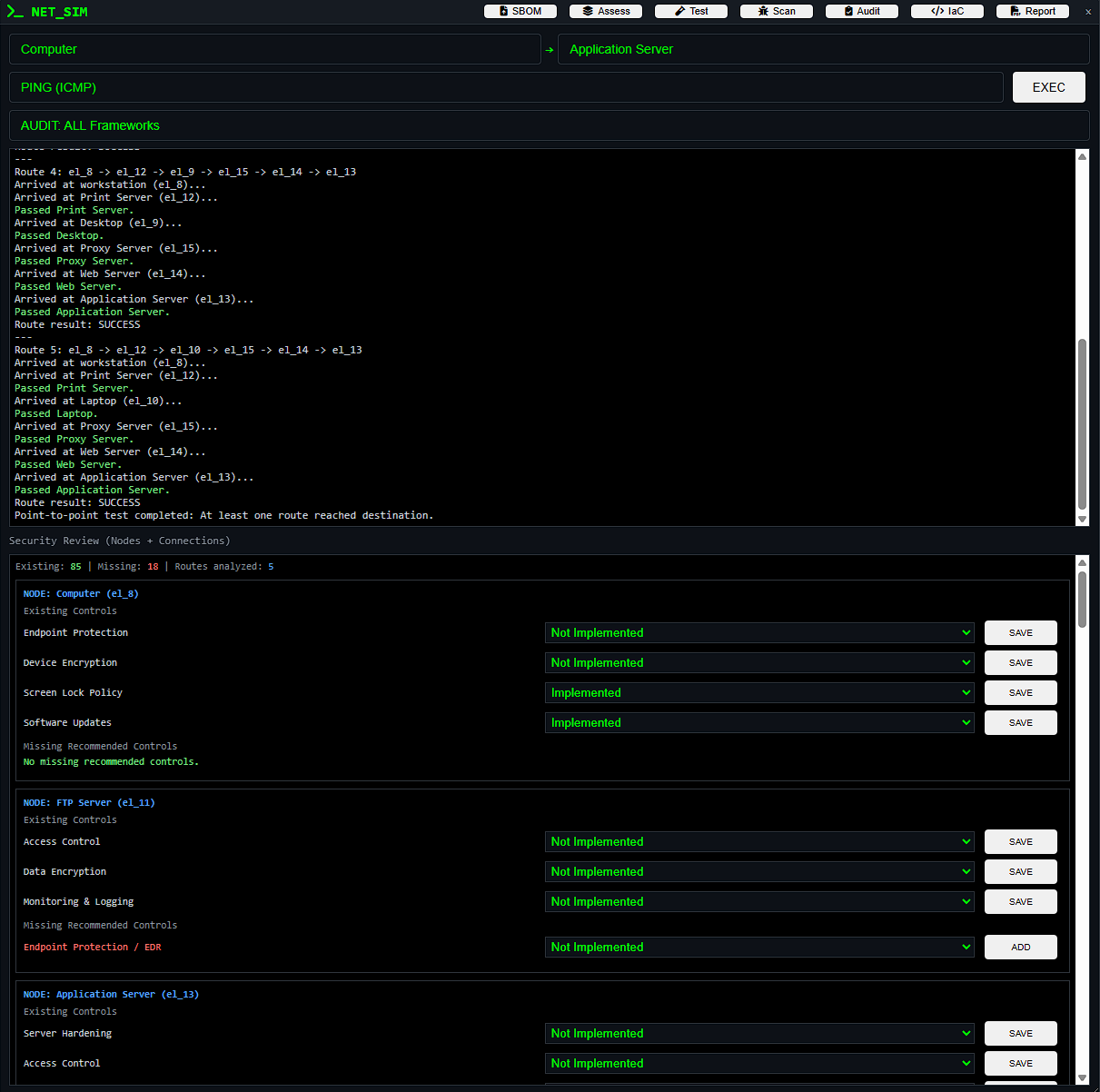
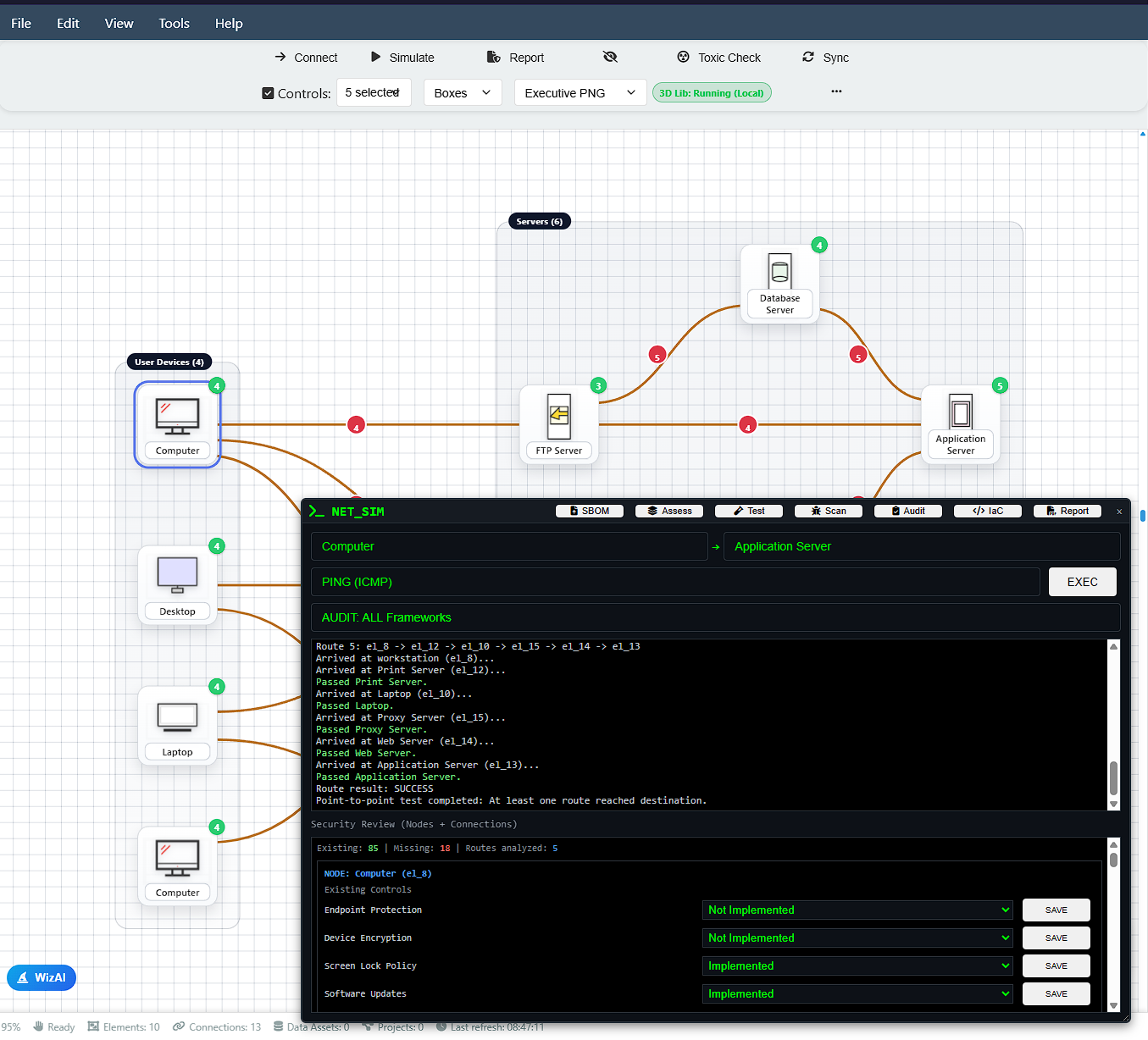
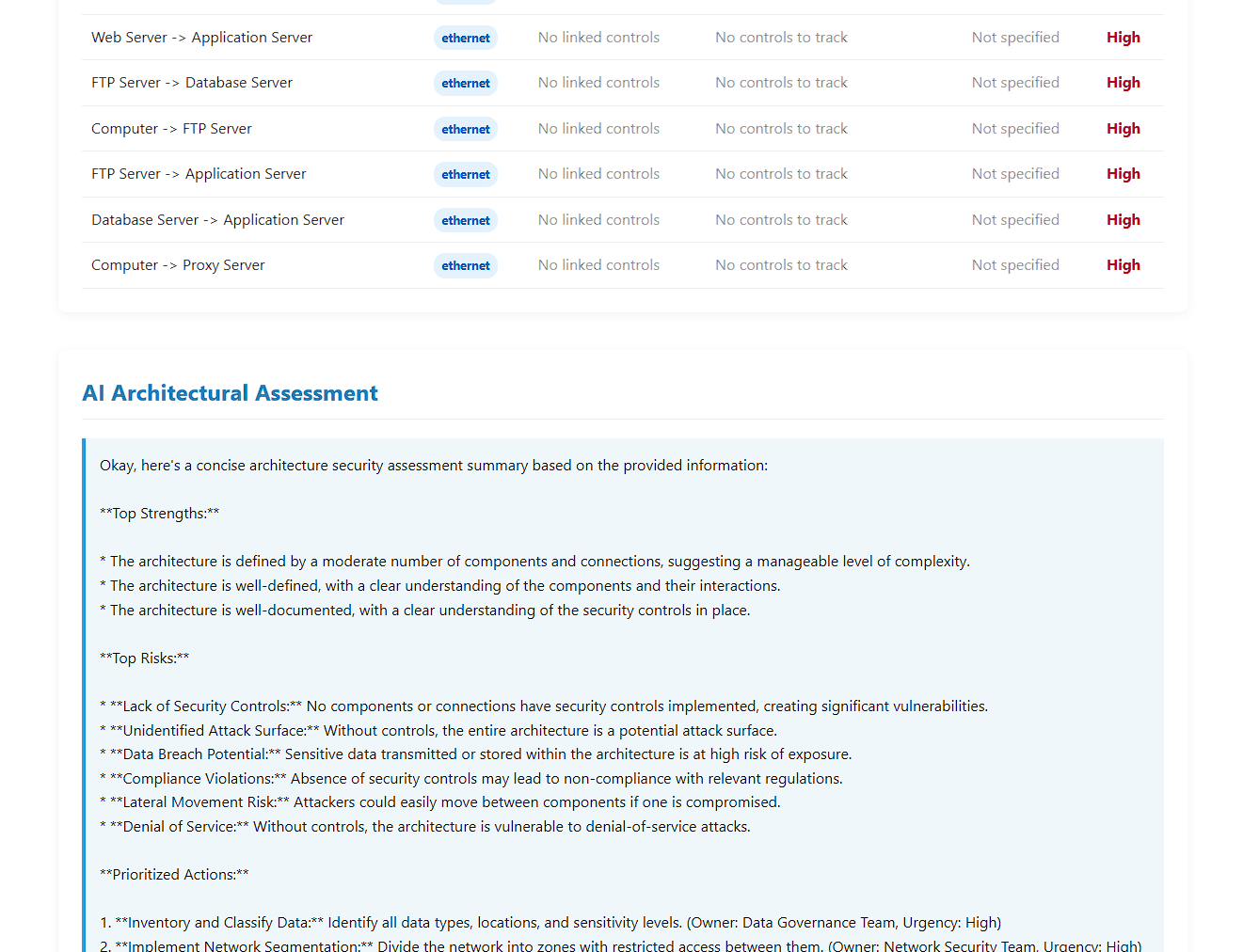
Map, validate, and track controls across components and connections.
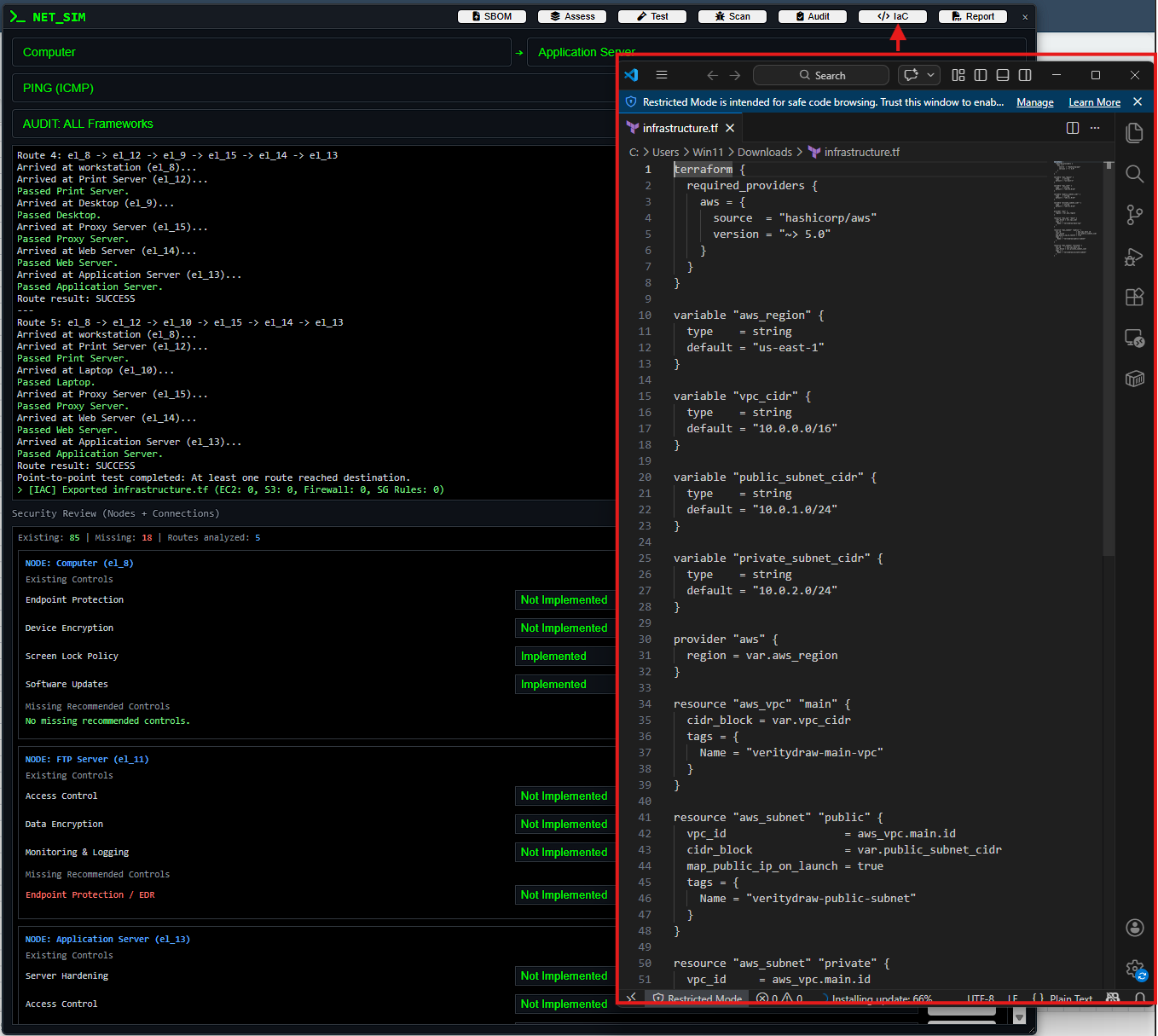
Move from design to implementation with export and cloud integration workflows.
Real product screens from your current VerityDraw environment.
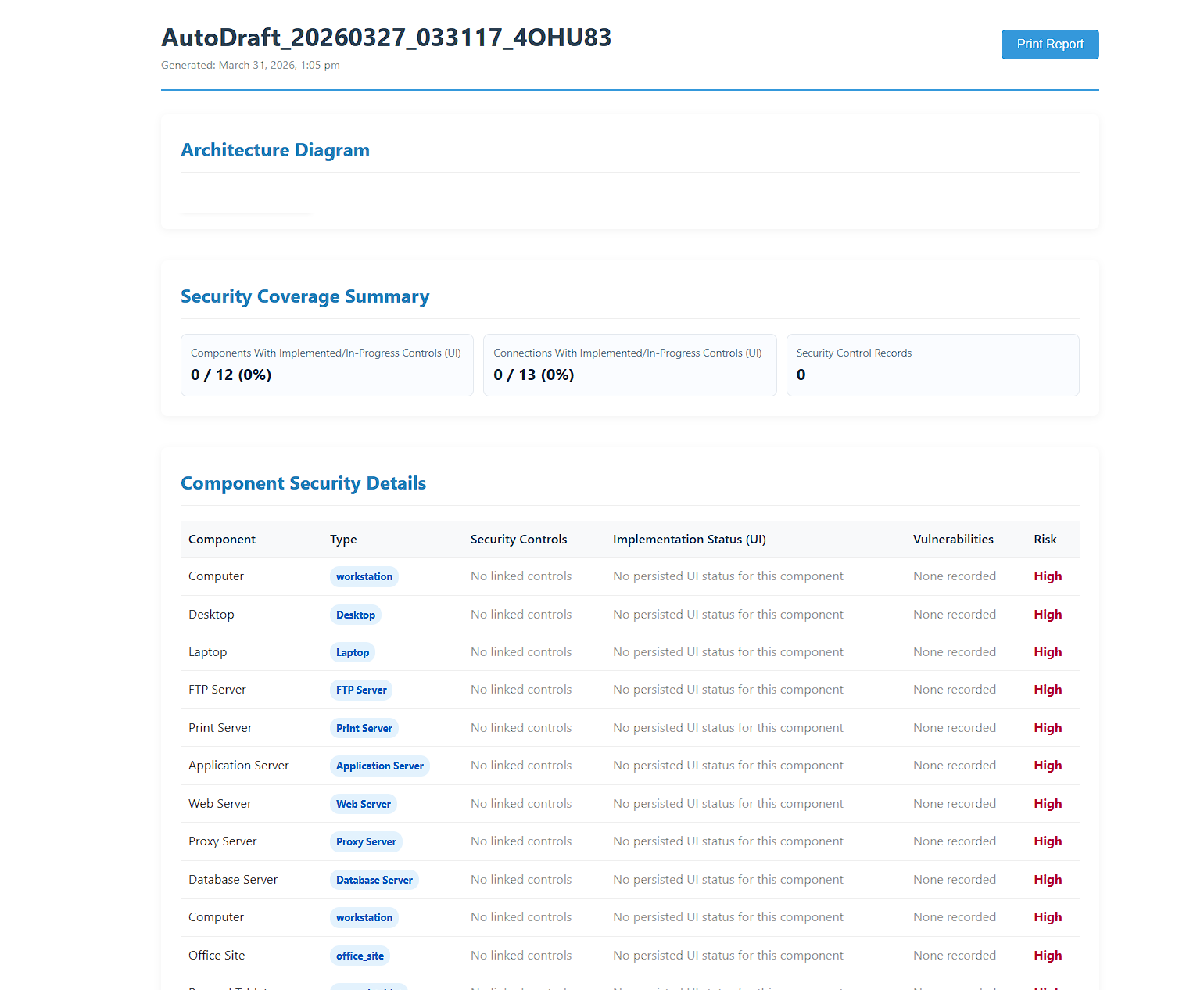
Fast path from architecture draft to validated security outcomes.
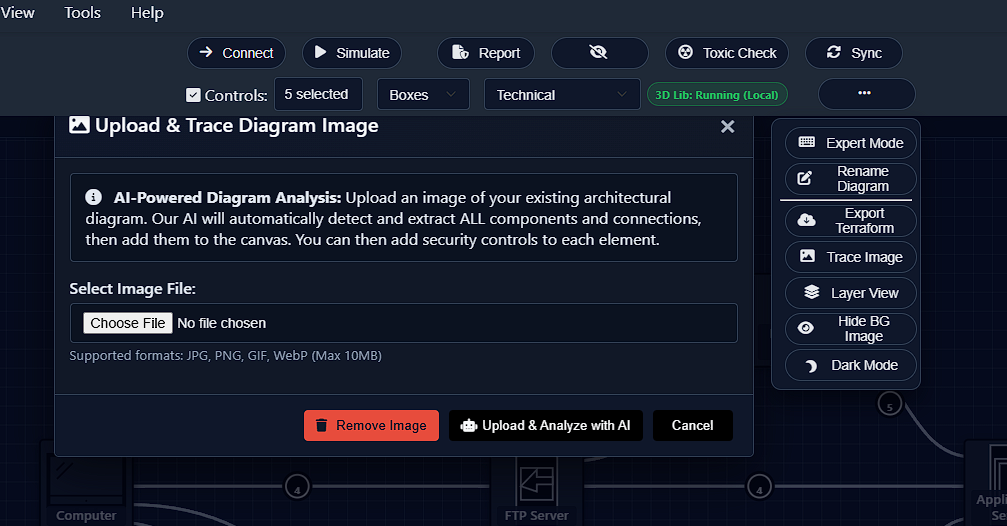
Create or import architecture diagrams with rich system and data context.
Run threat simulation and security audits to expose risk paths and control gaps.
Apply controls, document decisions, and align remediation to policy requirements.
Export artifacts, generate reports, and integrate with cloud + IaC workflows.
Submit feature requests, ideas, and bug reports directly to your backend endpoints.
Share what should improve next in VerityDraw.